Security at Float
Built from the ground-up with financial control at the centre of everything we do.
How Float Keeps You Protected
Float is SOC 2 Type 2 and PCI-DSS compliant and committed to the
highest level of security and industry standards.

End-to-end data encryption
Float uses advanced security measures that ensure the confidentiality, integrity, and protection of all sensitive data including TLS 1.2 or higher encryption of sensitive data, penetration testing, and vulnerability assessments.

Zero fraud liability protection
Float has you covered so you’re not responsible for fraudulent transactions. Plus, our intelligent software can detect fraud patterns and identify inconsistent behaviour so you’re notified immediately.

Effortless dispute resolution
If you’re the victim of fraud, you can get funds back in as little as 3 business days. You can easily submit a dispute directly in-app and our team will work with you to resolve disputes and ensure your cards are protected.
Funds Held
Securely




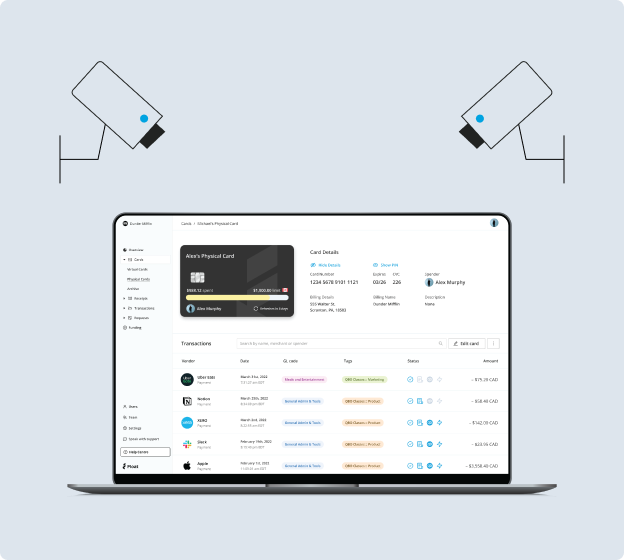
Product Security
Float’s smart corporate cards are powered by intelligent spend management software that give your team control over who spends what and real-time visibility into transactions.
With Float, you can prevent fraud before it happens and pause or cancel cards at any time.
Payment Security
Float is PCI-DSS certified, meaning we abide by the highest standard of security in the storage, processing, and transmission of cardholder data.
With advanced fraud detection and prevention protocols, 24/7 fraud monitoring, and 3D Secure, you can rest easy knowing your company spending is with Float.
User Management
Float keeps your accounts safe with multi-factor authentication and SAML single sign-on.
With dynamic approver roles and HRIS integrations, you can easily manage the employee lifecycle and ensure only authorized users have access to Float.
Our Security Framework
Security is one of the most important things we do – here’s our framework to comply with industry standard controls and ensure the highest level of security.

Least privilege
Access to organizational resources and information should be granted on a need-to-know basis.

Defense-in-depth
Organizational security is layered to provide multiple levels of protection.

Risk management
Organizational security is based on an assessment of the potential risks and threats faced by Float.

Compliance
Float complies with all applicable laws, regulations, and industry standards related to security.
Product Security
We are continuously implementing security measures that ensure the confidentiality, integrity, and protection of all sensitive data.
Float abides by the highest standard of security in the storage, processing, and transmission of cardholder data. We worked with a Qualified Security Assessor to confirm that we comply with the requirements under PCI-DSS and receive our PCI-DSS SAQ D Report & Attestation of Compliance (AOC).
Float implements encryption, access control, and monitoring to mitigate risks of digital storage not actively being processed or transmitted.
Float uses TLS 1.2 or higher encryption to transmit data. Server TLS keys and certificates are managed through AWS.
Float engages with industry leaders Detectify for penetration tests, who are a fully automated External Attack Surface Management solution powered by a world-leading ethical hacker community.
Float undergoes vulnerability scanning at key stages of our Secure Development Lifecycle (SDLC) to actively monitor threats, including network vulnerability scanning on a period basis, malicious dependency scanning to prevent the introduction of malware into our software supply chain, and Intrusion Detection & Prevention powered by AWS GuardDuty.
Corporate Security
Float is committed to ensuring the highest standards of security tools and training for our product and team.
Float successfully completed the AICPA Service Organization Control (SOC) 2 Type 2 audit. The audit confirms that Float’s information security practices, policies, procedures, and operations meet the SOC 2 standards for security.
Float uses Okta to secure our identity and access management. Float employees are granted access to applications based on their role. Access must be approved according to the policies set for each application.
We have implemented firewalls to protect our systems from unauthorized access. Our firewalls are regularly updated to ensure they are up-to-date and provide the highest level of protection.
Our systems are updated regularly with the latest security patches to ensure that any vulnerabilities are addressed promptly.
Our employees receive regular training on security protocols and best practices to ensure they are aware of potential security risks and how to mitigate them.
Float uses a risk management approach to vendor security. Vendors are reviewed and evaluated regularly based on access to customer and corporate information, integration with production environments, and reputational damage. All vendors that we engage with have completed an information security assessment standard such as: SOC 2 or ISO 27001 certification.
Contact Us
Float is always open to feedback, questions, and
suggestions – email us at security@floatcard.com